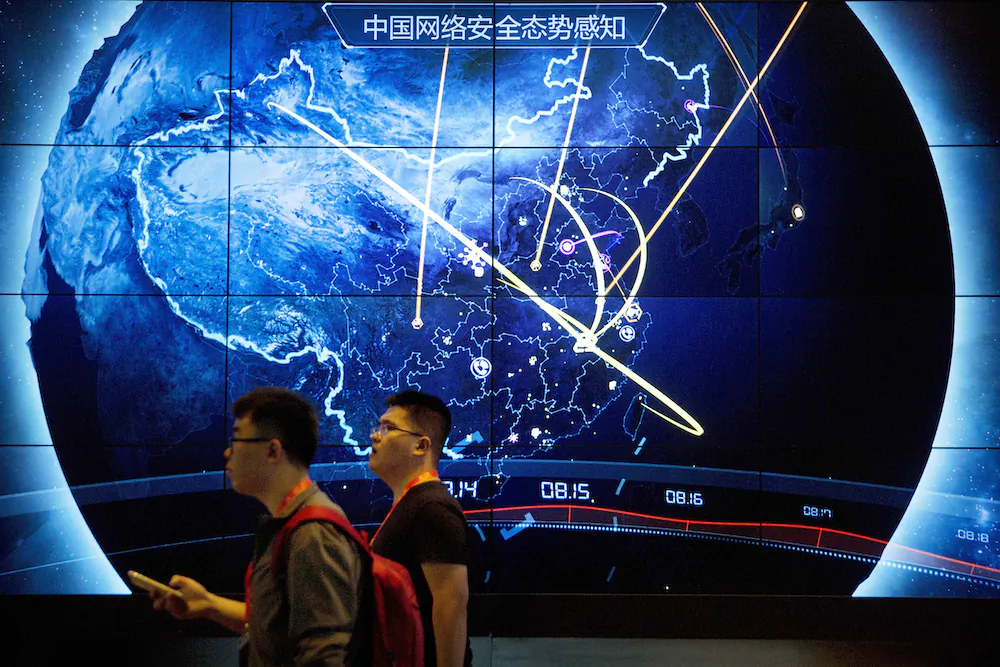
Attendees walk past an electronic display showing recent cyberattacks in
China at the China Internet Security Conference in Beijing on Sept. 12,
2017. (Mark Schiefelbein/AP Photo)
Suspected state-backed Chinese hackers used a security hole in a popular email security appliance to break into the networks of hundreds of public and private sector organizations globally, nearly a third of them government agencies, including foreign ministries, cybersecurity firm Mandiant said Thursday.
“This is the broadest cyber espionage campaign known to be conducted by a China-nexus threat actor since the mass exploitation of Microsoft Exchange in early 2021,” Charles Carmakal, Mandiant’s chief technical officer, said.
The hack exploited a software vulnerability in Barracuda Networks’ Email Security Gateway, compromising tens of thousands of computers globally.
The hacking began on Oct. 10, 2022, but the intrusions were only discovered by Barracuda on May 19, 2023. Counter-measures were promptly taken.
In response, the hackers immediately altered their malware and employed persistent, high frequency hacking attacks, targeting a number of victims located in at least 16 different countries.
On May 23, Barracuda asked Mandiant to investigate the hacking.
On June 6, Barracuda reiterated its advice to its impacted customers to “immediately isolate and replace compromised appliances.”
In an emailed statement Thursday, Barracuda said about 5 percent of its active Email Security Gateway appliances worldwide showed evidence of potential compromise. The company stated that it was providing replacement appliances to affected customers at no cost.
Mandiant’s investigation concluded with “high confidence” that the hackers were an organized team engaged in “espionage activity in support of the People’s Republic of China,” calling the hacking team an “aggressive and highly skilled actor.”
The hackers sent emails containing malicious file attachments to gain access to targeted organizations’ devices and data, Mandiant said. Of those organizations, 55 percent were from the Americas, 22 percent from Asia Pacific, and 24 percent from Europe, the Middle East, and Africa combined. Targets included foreign ministries in Southeast Asia, foreign trade offices, and academic organizations in Taiwan and Hong Kong, the company said.
Mandiant explained the majority impact in the Americas due to it being Barracuda’s main customer base.
The hackers operated at both the organizational and individual account levels and focused on issues that are high policy priorities for China, particularly in the Asia Pacific region, Mandiant said. The hackers searched for email accounts of people working for governments of political or strategic interest to China at the time they were participating in diplomatic meetings with other countries.
Mandiant said its investigation involved cooperation with multiple governments and intelligence agencies, commended Barracuda for its “decisive actions, transparency, and information sharing,” and provided its client with further “hardening, remediation and hunting” recommendations.
The Associated Press contributed to this article.
From NTD News
No comments:
Post a Comment